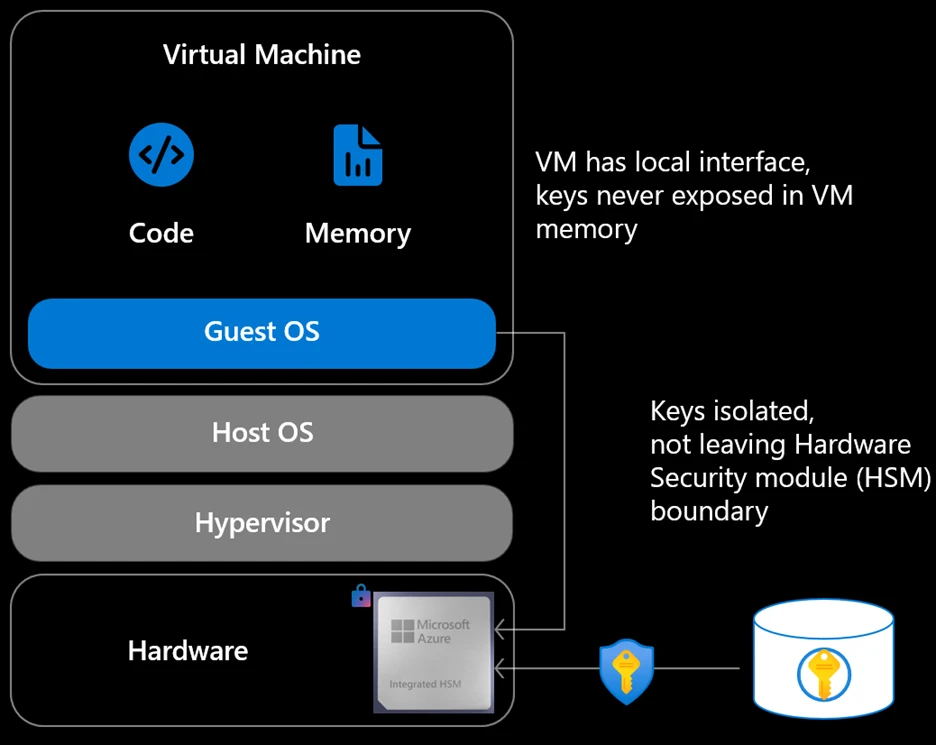
In this article Defense in depth as a system Secure by design: Engineering security into the platform Hardware and host-level trust Virtual machine-layer trust Secure by default: Protection enabled without friction Secure defaults across networking Encryption and data protection by default Compute protection defaults Secure in operation: Continuous protection at runtime Monitoring, detection, and signal correlation Identity-centric control and least privilege Bringing defense in depth and SFI together Security as an ongoing platform commitment This blog post is the third part of a blog series called Azure IaaS which will share best practices and guidance to help you build a trusted infrastructure platform—from performance, resiliency, and security to scalability and cost efficiency . Security for cloud infrastructure is no longer defined by a single control, product, or boundary. Modern threats target identity, software supply chains, control planes, networks, and data simultaneously. Addressing this reality requires two things to work together: a layered defense-in-depth architecture and security principles that are enforced consistently across the platform . In Azure Infrastructure as a Service (IaaS) , security is built around these two reinforcing ideas. First, Azure implements defense in depth , applying multiple, independent layers of protection across compute, networking, storage, and operations so that no single control stands alone. Second, those protections are guided by Microsoft’s Secure Future Initiative (SFI) principles: secure by design, secure by default, and secure in operation . Together, they define how Azure IaaS is engineered, configured, and operated at scale. Explore Azure IaaS solutions Defense in depth as a system Defense in depth is not a checklist of features—it is a system-level security architecture . Each layer is designed with the assumption that another layer may fail, and that compromise at one point should not lead to platform-wide impact. In Azure IaaS , defense in depth spans the full infrastructure stack: Hardware and host integrity Virtualized compute isolation Network segmentation and traffic control Data protection for storage Continuous monitoring and response These layers are intentionally independent. Hardware root-of-trust mechanisms validate host integrity before workloads ever start. Virtual machines (VM) run with strong isolation boundaries enforced by the hypervisor. Network controls limit lateral movement and restrict exposure. Storage services encrypt and protect data even if credentials are compromised. And telemetry and monitoring systems operate continuously, detecting and responding to anomalous behavior across the platform. This layered approach ensures that Azure IaaS security does not rely on perimeter assumptions or a single “control plane defense,” but instead applies multiple mutually reinforcing controls that work together. Build a stronger cloud infrastructure with Azure IaaS Secure by design: Engineering security into the platform “Secure by design” means security is architected into the platform from the beginning , not added after deployment. In Azure IaaS , this starts at the lowest layers of the stack. Hardware and host-level trust Azure servers are built with hardware roots of trust , measured boot, and secure firmware validation. Technologies such as Trusted Platform Modules (TPMs) and secure boot validate that host firmware, boot loaders, and operating systems have not been tampered with before the system joins the Azure fleet. These mechanisms reduce exposure to firmware-level and boot-chain attacks that traditional software-only defenses cannot address. Azure also offloads critical infrastructure functions—such as storage, networking, and management operations—into dedicated, hardened components like Azure Boost , reducing the attack surface of the host operating system and improving isolation between customer workloads and platform services. Virtual machine-layer trust At the virtual machine layer, Azure enforces strong virtualization boundaries using a hardened hypervisor. Features like Trusted Launch for Azure VM combine secure boot, virtual TPMs, and integrity monitoring to protect VMs against low-level attacks such as bootkits and kernel rootkits. For highly sensitive workloads, Azure confidential computing extends defense in depth by using trusted execution environments (TEEs) backed by hardware-based memory encryption (such as AMD SEV‑SNP or Intel TDX). These technologies help ensure that data remains protected even while in use and inaccessible to the host or hypervisor. Security here is not a bolt-on—it is a design property of how Azure compute infrastructure is built and operated. Secure by default: Protection enabled without friction Secure-by-default controls reduce risk by making the safest option the standard configuration , without requiring customers to assemble security from scratch. Learn how to keep critical applications running with built-in resiliency at scale with Azure IaaS Secure defaults across networking In Azure IaaS , networking defaults are aligned with least-privilege and Zero Trust principles. Virtual networks are isolated by default. Inbound traffic to VM is blocked unless explicitly allowed. Network security groups (NSGs) enforce stateful filtering, while Azure Firewall provides centralized policy enforcement and traffic inspection when deployed. Private connectivity options such as Azure Private Link and private endpoints allow services to be accessed without exposing them to the public internet. DDoS protection is automatically applied at the platform edge, helping protect workloads from volumetric attacks without additional configuration. These defaults limit exposure by design, narrowing the attack surface before workload-specific rules are added. Encryption and data protection by default Azure IaaS storage services encrypt data at rest by default , using platform-managed keys,
Originally published at azure.microsoft.com